Most new online business owners spend their early weeks thinking about the same things — getting traffic, making the first sale, figuring out whether the pricing is right, whether the homepage looks professional enough. Security doesn’t make that list. Not because nobody cares, but because it doesn’t feel relevant when you’re still trying to get anyone to notice you exist.
The problem is that relevance and risk aren’t the same thing.
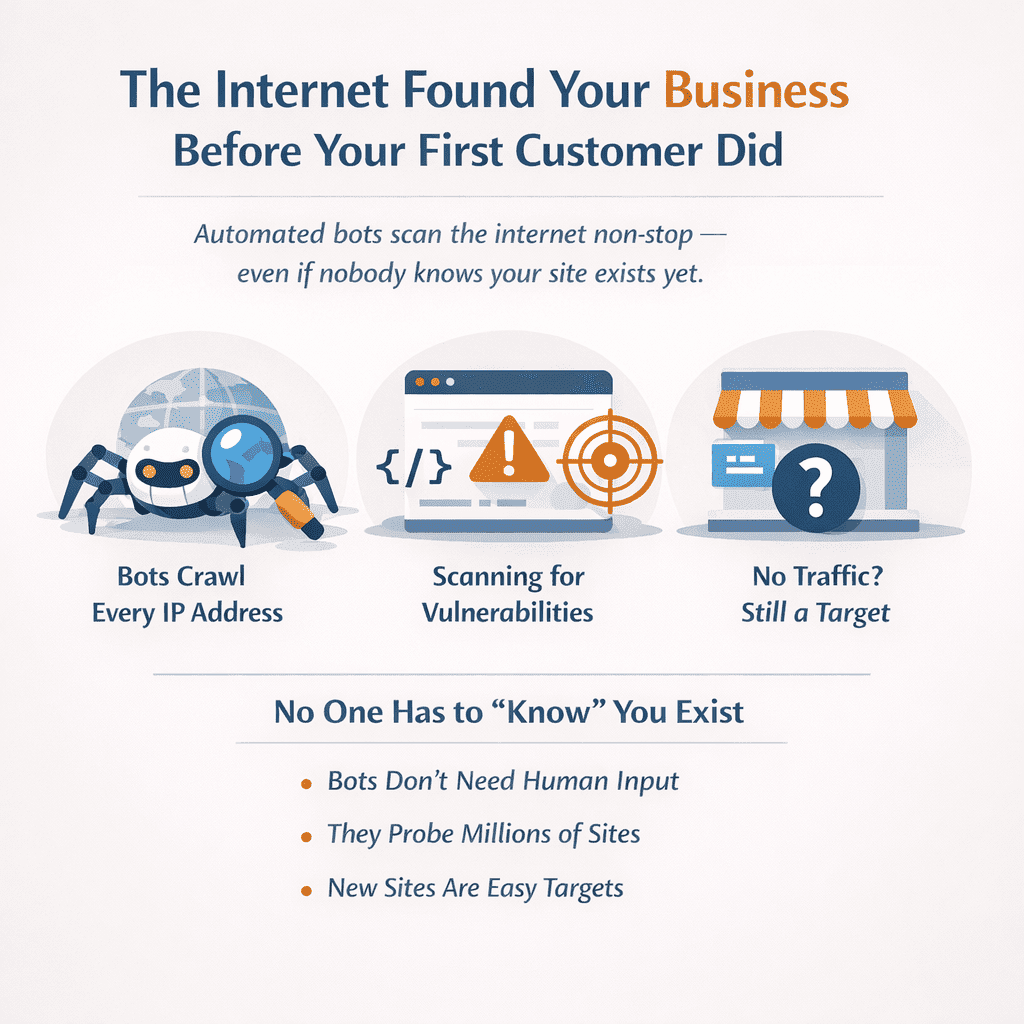
Every online business is a security target from the moment it goes live — not after it becomes profitable, not after it starts appearing in search results, not after someone decides it’s worth the effort. From day one. The automated systems continuously scanning the internet for vulnerabilities don’t look up your revenue or check your monthly visitor count first. They just find the opening and log it.
What follows is not a scare piece. It’s an honest look at why the “I’m too small and unknown to be a target” assumption is the most expensive one a new online business owner can make — and what actually closing that gap looks like for someone running a lean operation without an IT department or a security budget.
Table of Contents
The Internet Found Your Business Before Your First Customer Did
Here’s something that doesn’t get said enough to people starting an online business: your site was scanned for vulnerabilities before most people even knew it existed.
Not by a competitor. Not by some sophisticated hacker who read your launch announcement. By automated bots that crawl the internet continuously, indiscriminately, hitting every IP address they can reach — including yours, probably within hours of your site going live.
That’s not speculation. It’s just how the internet works.
The reason this matters is that most new business owners are operating on an assumption that feels logical but is actually dangerous: the idea that being small and unknown keeps you safe. If nobody knows you exist, who’s coming after you, right? The problem is that logic only applies to humans. Bots don’t Google you first. They don’t check your Instagram following or look up your monthly revenue. They’re running scripts that probe for weaknesses across millions of sites at once, and your brand-new online business is sitting in that pool whether you like it or not.
What these bots are looking for isn’t always obvious either. People assume attackers want something dramatic — credit card numbers, a database full of customer records. Sometimes, yes. But a brand-new site with barely any traffic still has things worth taking: your hosting environment can be hijacked to send spam, your site can be quietly redirected to serve malware to whoever does eventually visit, your contact forms can be weaponized. The attack doesn’t have to be about you specifically to cause you real damage.
The timing is what makes this particularly uncomfortable. That early window — between launching and actually building any kind of audience — tends to be when online businesses face the highest security risk precisely because that’s when the setup is most rushed and most incomplete. Default configurations nobody changed. Plugins installed quickly and never revisited. No backup system yet because “I’ll set that up properly later.” Every one of those gaps is something an automated scan can find and log.
And here’s the thing nobody really talks about: you don’t get a warning. There’s no notification that says “hey, your site was just probed 47 times this morning.” It happens in the background, silently, while you’re writing product descriptions or figuring out your pricing. By the time something actually goes wrong, the initial reconnaissance happened weeks ago.
This isn’t meant to be alarming for the sake of it. But the old idea that obscurity is a form of protection — that if you’re small enough and quiet enough, you’ll fly under the radar — genuinely does not apply to automated threats. The radar, in this case, is pointed at everything.
You Don’t Have to Be Interesting to Be a Target
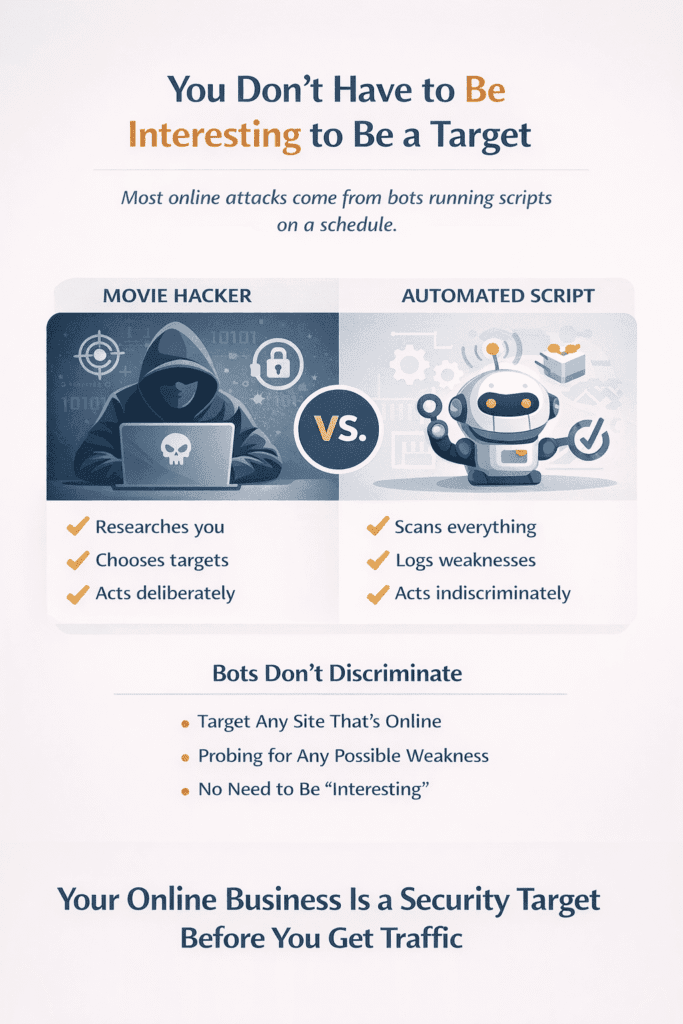
People imagine hackers the way movies taught them to — someone in a dark room, researching targets, deciding who’s worth their time. That image is so embedded in how we think about cybersecurity that it shapes decisions business owners make without even realizing it. If nobody’s coming after me specifically, I’m fine. It’s a reasonable assumption. It’s also wrong in a way that matters.
Most of what threatens a small online business today isn’t a person making a decision. It’s a script running on a schedule.
That distinction is everything. A person might look at your business and conclude you’re not worth the effort. A script doesn’t conclude anything — it just runs, checks for weaknesses, logs what it finds, and moves on to the next IP address. There’s no evaluation happening. No threshold of success you need to cross before you become relevant. The moment your site is live, it’s in the pool. Whether it gets flagged depends entirely on whether it has an exploitable weakness — not on whether you’re interesting.
This is where the “I’m too small to be a target” assumption quietly falls apart. It’s not that the assumption is completely wrong — a genuinely sophisticated, human-led attack probably isn’t coming for a business with eleven customers and a half-finished about page. But sophisticated human-led attacks are not the primary threat to most small online businesses. Automated opportunistic attacks are. And those operate on completely different logic.
What attackers running these campaigns actually want from a small site is often not what you’d expect. Yes, sometimes it’s customer data. But just as often it’s your server resources — hijacked quietly to send spam, run phishing campaigns, or mine cryptocurrency in the background while you’re none the wiser. Your business isn’t the prize in that scenario. Your infrastructure is. And infrastructure is something every online business has from day one, regardless of how unknown or unestablished it is.
This is the core reality most founders don’t sit with long enough — every online business is a security target, not because of what it’s worth, but because of what it hasn’t locked down. That’s the actual filter being applied. Not revenue. Not reputation. Not traffic. Just — is there an opening? For a business that launched recently, with default settings still in place and security configured loosely if at all, the honest answer is often yes.
The uncomfortable part isn’t that this happens. It’s that it happens quietly, without warning, and usually well before the business owner has even thought to ask the question.
Early-Stage Businesses Have a Specific Kind of Vulnerability Nobody Talks About
Most cybersecurity advice is written for businesses that already have something resembling infrastructure — a team, a system, maybe someone whose job title includes the word “operations.” It’s reasonable advice. It’s just not written for someone who built their online store in a weekend by following a YouTube tutorial and copy-pasting what seemed to work for someone else in a Reddit thread.
And that’s most new online businesses.
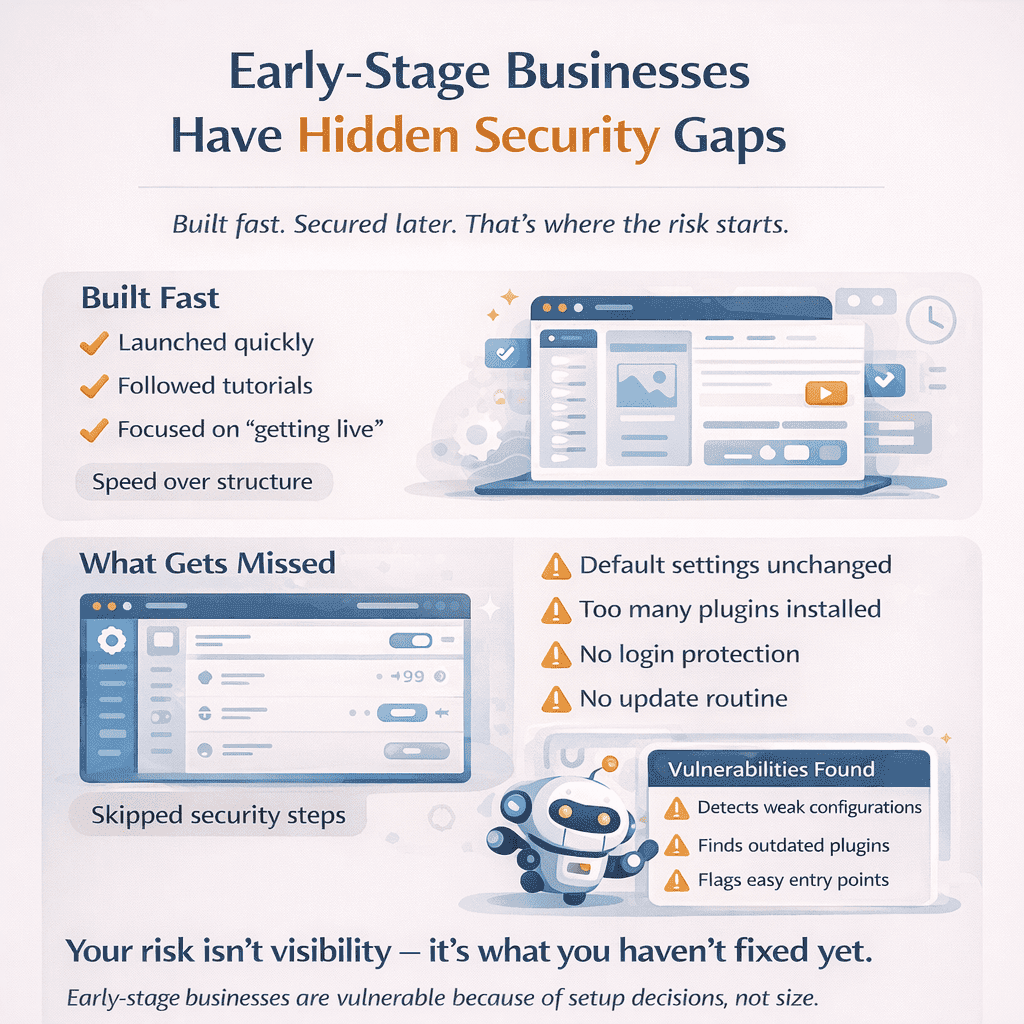
The vulnerability that early-stage businesses carry isn’t just about having fewer resources — it’s about how they were built in the first place. Every decision made during setup was optimized for one thing: getting something live. Getting it working. Getting it in front of people before the motivation ran out or the window closed. Security doesn’t naturally surface in that process — not because founders are reckless, but because nothing in the typical setup experience prompts you to think about it.
Platform setup wizards don’t warn you that the default configurations you just clicked through are convenient rather than safe. Plugin installation pages don’t mention that the tool you just added has permissions it doesn’t actually need to do its job. The entire onboarding experience for most online business platforms is built around reducing friction — and security, almost by definition, adds friction. So it gets quietly deprioritized, often without the founder even realizing a choice was made.
What you end up with is a business that looks fine from the outside and has real gaps baked into its foundation. The admin username is still the default. The login page accepts unlimited password attempts with no lockout. The contact form plugin hasn’t been updated in four months because nobody remembered it was there. None of these feel urgent when you’re chasing your first ten customers. All of them show up immediately in an automated vulnerability scan.
This is the part nobody talks about enough — the tool sprawl that accumulates in the first few months of running an online business. It starts reasonably. An SEO plugin here, a popup builder there, something someone recommended in a Facebook group that you installed, used twice, and completely forgot about. Each of those tools is a potential entry point. Each has its own update cycle and its own security history. Abandoned plugins — the ones sitting inactive on your site because you moved on to something else — are quietly one of the most common ways early-stage sites get compromised. They stop receiving attention, vulnerabilities get discovered by researchers or attackers, and they just sit there waiting.
The trade-off is real and worth acknowledging honestly. Moving fast in the early days isn’t just understandable — it’s often the right call. A business that stalls at launch because the founder is perfecting security configurations is not a successful business. But there’s a difference between moving fast and never circling back. That gap between “I’ll sort the security stuff properly once things settle down” and actually doing it tends to stretch far longer than anyone intends. Weeks become months. The site grows. More tools get layered on top of an already shaky foundation. And the original setup — rushed, default-heavy, and never revisited — just keeps running underneath all of it.
The specific vulnerability of an early-stage online business isn’t dramatic. It’s just neglect that started on day one and never got corrected.
The Habits That Leave the Door Open (And Feel Completely Normal)
Nobody running a small online business thinks of themselves as someone who takes security lightly. And genuinely, most don’t — not intentionally. The habits that create the most exposure aren’t the ones that feel risky. They’re the ones that feel like common sense.
Start with password reuse, because it’s everywhere. If you’ve ever set up a new business account and used the same password you use for three other things because you were in the middle of something and just needed to get past the signup screen — that’s the habit. Most people who do this know, on some level, that it’s not ideal. They also know they’ll sort it out properly at some point. The problem is that “at some point” is doing a lot of work in that sentence. Meanwhile, data breaches happen constantly — not just to small platforms, but to large, well-resourced ones. When any one of those platforms gets breached and your credentials are in the dump, every other account using that same password is now accessible. Not theoretically. Actually.
The contractor access problem is quieter but arguably worse. You hire a freelancer to set up your site, give them admin access, the project wraps up, and then — nothing. The access question just never comes up. Not because you decided to leave it open, but because the offboarding conversation didn’t happen and there was always something more pressing to deal with. What you’re left with is a former contractor — someone you may have had a perfectly fine working relationship with — who still has full access to your business. Most of the time this is fine. Occasionally it isn’t. And the uncomfortable part is you probably can’t say with certainty right now who has active access to your accounts.
Two-factor authentication gets skipped for a reason that’s completely understandable and completely irrelevant to whether it protects you. The reasoning usually goes: I’m on my own laptop, my own network, I know it’s me — why do I need a second step? That logic holds up if the threat is someone physically taking your device. It doesn’t hold up against credential stuffing attacks, where stolen username and password combinations from unrelated breaches get tested against thousands of platforms automatically. In that scenario, 2FA is the only thing standing between a leaked password and a fully compromised account. The extra thirty seconds per login is genuinely the point.
Updates are their own category of procrastination. The notification sits there, you click “remind me later,” and later becomes a week, then a month. What most people don’t realize is that security updates are released in response to discovered vulnerabilities — which means the vulnerability is already public by the time the update exists. Security researchers find it, report it, the platform patches it, and the patch announcement effectively tells every attacker exactly what to look for in unpatched installations. The window between patch release and active exploitation is short. Sitting on pending updates isn’t a neutral position — it’s an increasingly exposed one with each passing day.
This is the part worth being direct about. Every online business is a security target — not because of what it’s worth or how visible it is, but because of the everyday habits that quietly keep the door open. That’s what makes this harder to fix than it sounds. If these habits felt dangerous, people would change them immediately. Instead they feel like the normal, practical choices of someone managing a hundred things at once. Which is exactly the condition that lets them persist indefinitely.
What actually helps isn’t a complete security overhaul attempted on a Sunday afternoon. That approach usually ends with half-finished changes and a false sense of having dealt with it. The more honest approach is to pick the single habit creating the most exposure right now and fix just that. For most online businesses that’s password reuse on critical accounts — hosting, domain registrar, payment processor. Close that gap first. Everything else can follow in order of actual consequence rather than theoretical completeness.
The risks don’t announce themselves. They just accumulate, quietly, in decisions that felt completely reasonable at the time.
Why Fixing It Once Fixes Nothing
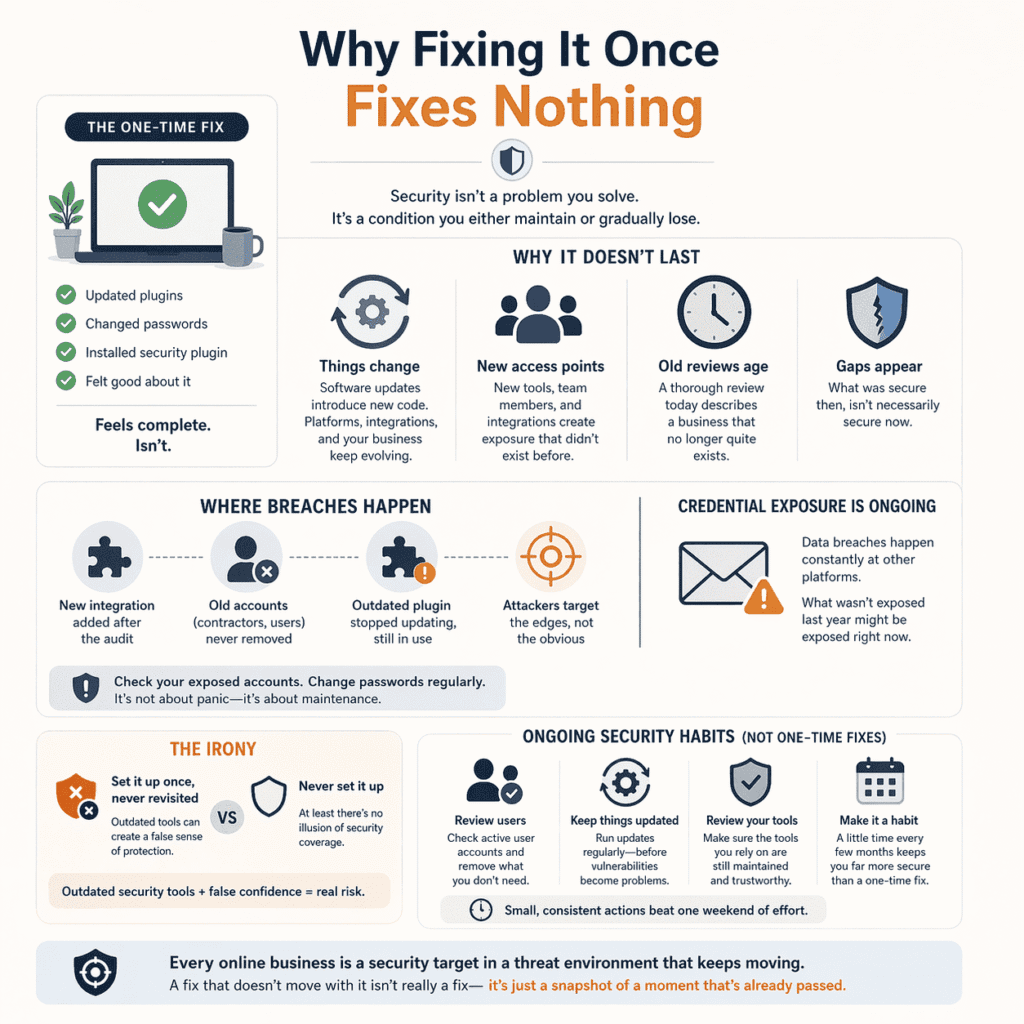
At some point, most online business owners do the thing. They spend a weekend going through their security setup, update the plugins, change some passwords, install a security plugin, and close the laptop feeling like the problem is handled. That feeling is real. The problem is that it’s based on a version of security that doesn’t actually exist.
Security isn’t a problem you solve. It’s a condition you either maintain or gradually lose.
The one-time fix works on an assumption nobody states out loud — that the threat environment you secured against today is the same one you’ll face in six months. It won’t be. Software gets updated, and updates introduce new code, and new code occasionally introduces new vulnerabilities. Platforms change their integrations. Your own business changes — new tools, new team members, new access points that didn’t exist when you last thought carefully about any of this. The security review that was genuinely thorough at the time becomes a description of a business that no longer quite exists.
This is the part that catches people off guard. The breach rarely happens at the point that received the most attention. It happens at the edge — the integration added after the audit, the old contractor account nobody thought to deactivate, the plugin that stopped receiving updates eight months ago but still seems to be working fine so nobody flagged it. Security attention naturally flows toward the obvious things. Attackers have figured this out. The periphery is where the actual exposure tends to live.
Credential exposure makes this worse because it’s ongoing by nature and completely outside your control. Data breaches at third-party platforms happen constantly — not occasionally, constantly. Your email address is sitting in breach databases from platforms you used briefly years ago and have long since forgotten. What wasn’t compromised last year might be compromised right now, and you’d have no way of knowing unless you checked. That’s not a reason to panic. It is a reason to treat password hygiene as something that needs revisiting periodically rather than something you sorted out once.
There’s a specific irony worth naming here. The businesses that did a security setup early and felt good about it are sometimes more exposed than the ones that never did one at all — because at least the latter group hasn’t developed a false sense of coverage. An outdated firewall plugin configured two years ago and never revisited isn’t necessarily doing what it was when it was installed. Security tools need maintenance too. Running outdated security tools while believing they’re protecting you is its own category of vulnerability.
What ongoing security actually looks like for a small online business isn’t a second full audit every quarter. It’s a small number of recurring habits that most people could fit into an hour every few months — reviewing active user accounts, running pending updates before they become critical, checking whether the tools you’re relying on are still actively maintained by someone. None of this requires technical knowledge. It requires the kind of consistency that’s genuinely harder to sustain than any single fix, because it doesn’t come with the same sense of closure.
Every online business is a security target in a threat environment that keeps moving. A fix that doesn’t move with it isn’t really a fix — it’s just a snapshot of a moment that’s already passed.
The Practical Part — Prioritized for Someone Running a Business Alone
Most security advice isn’t written for someone doing everything themselves. It’s written for organizations where security is at least partially someone’s job — where there’s a budget line for it, a person responsible for it, a meeting about it occasionally. If you’re handling your own customer service, your own fulfillment, your own bookkeeping, and your own marketing, the advice that begins with “implement a layered security strategy” belongs to a different conversation entirely.
Here’s what belongs to yours.
Get a password manager. Not as a background intention — actually do it this week. This is the highest-leverage security action available to a solo online business owner because it solves the password reuse problem almost completely, in one afternoon, without requiring any ongoing discipline beyond using it. The reason password reuse persists isn’t that people don’t know it’s bad. It’s that remembering unique passwords for forty different accounts is genuinely impossible without a system. A password manager is the system. There are free ones that are perfectly adequate. Paying for one costs less per month than a coffee. The time to set it up properly is a few hours. The protection runs indefinitely.
After that, two-factor authentication — but not on everything at once. That’s the version of this advice that leads to people abandoning it halfway through because it started feeling like a project. The accounts that matter most are the ones where a breach would be hardest to recover from: your hosting control panel, your domain registrar, your payment processor, your primary business email. Those four represent the majority of your actual exposure. Everything else can follow at whatever pace is realistic without it competing with running your business.
Backups are where most solo business owners discover they’ve been assuming something that isn’t true. The assumption is usually that the platform handles it. Sometimes it does — partially, with limitations buried in documentation nobody reads at setup. What platform backups typically cover is platform-level failures. They don’t necessarily cover the scenario where your account gets compromised and someone deletes or encrypts everything on their way out. An independent backup that lives somewhere separate from your primary hosting environment is the difference between a security incident being catastrophic and being recoverable. For most platforms this takes an hour to set up properly. It then runs in the background and requires almost no attention — until the day it’s the most important thing you ever configured.
Updates. Turn on automatic updates wherever the option exists. The objection that comes up most often is that automatic updates occasionally break something — a layout issue, a plugin conflict, something that needs fixing. That’s true and worth acknowledging. It’s also a recoverable problem in a way that running a compromised site for three months because you kept clicking “remind me later” is not. A broken footer takes an afternoon to fix. The other thing can take considerably more.
What you’ll notice about this list is that none of it requires technical knowledge. None of it requires hiring anyone. The barrier isn’t complexity — it’s that none of it feels urgent until something goes wrong, and by then the window for easy prevention has already closed. Every online business is a security target operating in a threat environment that doesn’t care about your workload or your bandwidth. The practical response to that isn’t paranoia — it’s just closing the gaps that are easiest to close first, before something else closes them for you.
Start with the password manager. Everything else follows from there.
Most Business Owners Only Take This Seriously After Something Goes Wrong
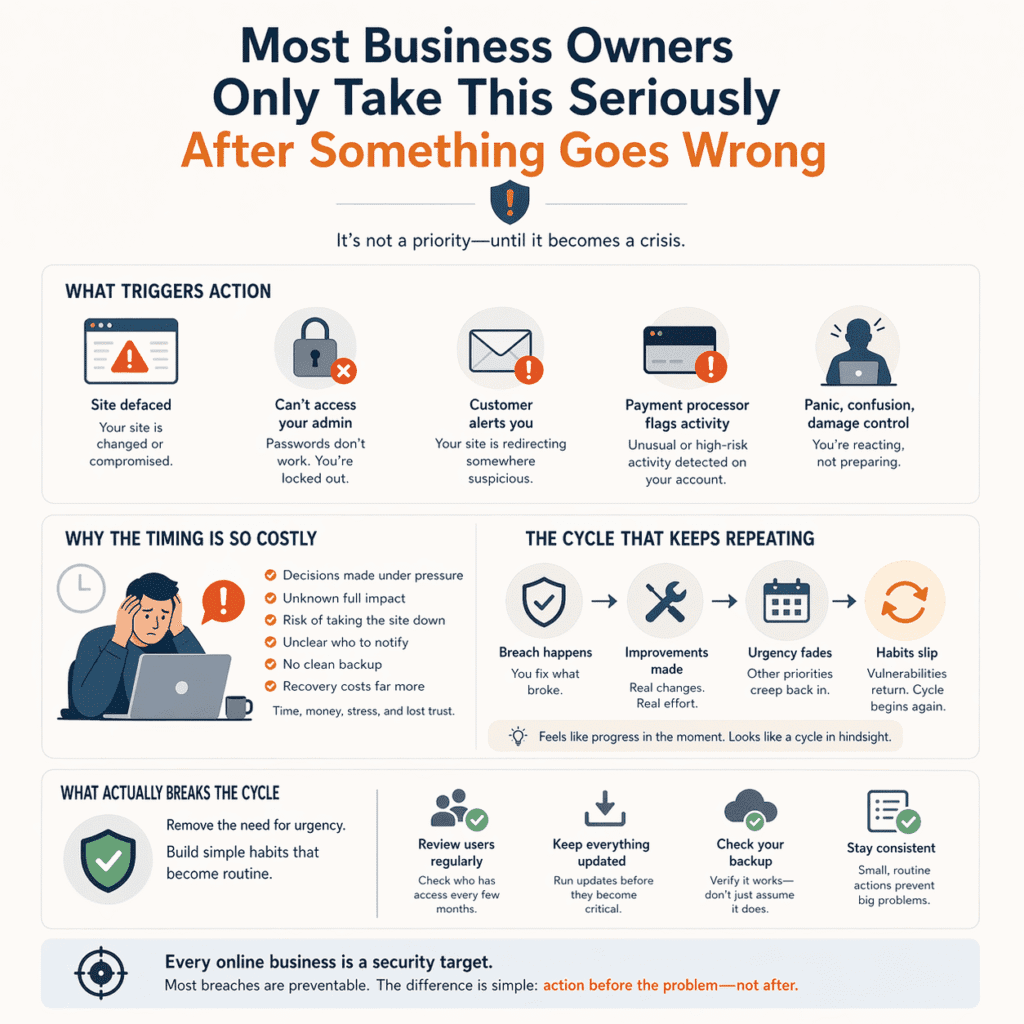
Nobody wants to hear this, but it’s probably the most accurate thing in this entire article. The typical trigger for a small online business owner taking security seriously isn’t an article, a statistic, or a warning from someone they trust. It’s waking up to find something has already gone wrong.
A site defaced. An admin password that no longer works. A customer email asking why your website is now redirecting to something suspicious. A payment processor flagging unusual activity. The security conversation most business owners have with themselves happens in the middle of one of these moments — panicked, under-prepared, trying to simultaneously figure out what happened, contain it, and keep the business from falling apart around them.
This isn’t unique to security and it isn’t a character flaw. It’s just how risk actually works for most people. Abstract future threats compete poorly against concrete present demands. A vulnerability that hasn’t caused a problem yet doesn’t feel like a problem yet — and a business that’s running fine, taking orders, sending emails, doing what it’s supposed to do, generates no signal that anything is wrong. The gap between “this could happen” and “this is happening” is invisible until it collapses.
What makes the timing so costly is that the aftermath of a breach is the worst possible environment for making good security decisions. You’re making choices under pressure, without preparation, often without knowing the full extent of what happened. Do you take the site down while you investigate? Do you notify customers? Do you know which customers? Do you even have a clean backup to restore from? These questions have answers — but they’re much better answered before the incident than during it. Every business owner who has been through this will tell you the same thing: the decisions made in that window are rarely the best ones, and the recovery costs — in time, money, and the kind of stress that doesn’t leave quickly — dwarf whatever prevention would have cost.
There’s a subtler version of this worth naming too. Some business owners do take a breach seriously, fix what broke, and make genuine improvements in the aftermath. And then, gradually, it fades. The urgency that drove the changes was real but it was temporary — and urgency, by nature, doesn’t last. Six months later the update notifications are being deferred again. The quarterly access review hasn’t happened since the breach. The new password policy is being followed by some people and ignored by others. Not because anyone stopped caring — because the felt sense of how bad it was has softened enough that other priorities have crept back in.
This is the pattern that’s hardest to break because it feels like progress while it’s happening and only reveals itself as a cycle in retrospect.
The thing that actually interrupts this cycle isn’t more urgency. It’s removing the need for urgency — building the recurring habits small enough and routine enough that they don’t require a crisis to motivate them. Checking active user accounts every few months. Running updates before they become critical. Verifying the backup actually works occasionally rather than assuming it does. None of this is demanding. All of it is easy to defer indefinitely without visible consequence — which is precisely the condition that makes every online business a security target in the first place.
The breach that prompts most business owners to finally take this seriously was preventable. Not always — sometimes things go wrong despite genuine preparation. But the incidents that hit most small online businesses aren’t sophisticated. They’re opportunistic. They succeed because the door was left open long enough for something to walk through it. Reading this is the easy part. Doing something before that happens is the part that actually matters — and the part that, statistically, most people don’t quite get to in time.
As Your Business Gets More Visible, So Does Your Risk
There’s a version of success that makes you more vulnerable in ways that are easy to miss while they’re happening. Growth brings traffic, tools, team members, integrations, platforms — and each of those things adds surface area to a security setup that was probably already stretched thin when the business was a fraction of its current size.
Most businesses don’t revisit their security posture as they grow. They just add things on top of what’s already there. The rushed, default-heavy foundation laid at launch ends up quietly supporting an operation it was never configured for — and nobody notices until something goes wrong.
Visibility changes the threat picture in a specific way that early-stage advice doesn’t prepare you for. Automated bots find your site regardless of size — that’s been true from day one, and it doesn’t change. But a business with real traffic, a recognizable name, and a public presence starts attracting a different kind of attention alongside the automated noise. People who’ve had a bad experience and want leverage. Competitors doing research that occasionally crosses lines. Someone who noticed your business is doing well and decided to look more carefully at how it’s put together. The larger you get, the more the threat mix shifts from purely opportunistic to occasionally deliberate — and deliberate attacks are a different problem than the automated ones this article started with.
Team access is where things get complicated fast. When it’s just you, access management is simple by default — you have the credentials, you know what’s connected to what, you make every decision. Add a virtual assistant, a developer, a social media manager, a fulfillment partner — and suddenly there are people with varying levels of access to your business, working on their own devices, on their own networks, with security habits you have no visibility into whatsoever. One person reusing a password that was exposed in an unrelated breach becomes your problem. One contractor whose laptop is compromised connects to your admin panel and brings whatever’s on that laptop with them. None of this requires bad intent — it just requires the normal messiness of people using technology the way most people use technology.
Then there’s the integration sprawl. What starts as a store connected to an email platform and a payment processor gradually becomes fifteen tools passing data back and forth — inventory management, a review aggregator, an affiliate tracker, a shipping integration, an accounting tool, something someone recommended in a podcast for recovering abandoned carts. Each connection is a potential entry point. Each third-party platform has its own security practices, its own breach history, its own vulnerabilities. You’re not just securing your own business at that point. You’re relying on the security culture of every company in that chain — most of which you know nothing about.
What you’ll notice, paying attention to how growing businesses actually experience incidents, is that the breach rarely traces back to the core of the business — it traces back to the edges. The integration that was added quickly without much thought. The contractor account that was never removed. The tool that stopped being actively used but stayed connected because disconnecting it never made it to the top of the list. Growth adds edges faster than most business owners can track them. Security that doesn’t keep pace with that accumulation isn’t really security anymore — it’s just the illusion of it.
The stakes attached to this change too, and it’s worth being direct about. A security incident when you have a hundred customers is painful and disruptive. The same category of incident when you have ten thousand customers — some of whose personal data, payment information, or purchase history you’re holding — is a different problem entirely. The legal exposure is different. The reputational damage is different. The recovery is different. The kind of incident that a tiny business weathers with a bad week can follow a larger business for years.
Every online business is a security target from day one — but what’s at stake when that targeting succeeds grows with everything else. The business that scales its revenue, its team, and its tool stack without ever scaling its security posture is building something increasingly worth protecting on a foundation that isn’t keeping up. That gap doesn’t announce itself. It just widens quietly until something makes it visible.